BEC, or Business Email Compromise is the most significant threat facing Real Estate organizations.
BEC involves attackers with stolen login credentials spoofing your organizations valid email accounts to manipulate payment wiring instructions and redirect funds to fraudulent accounts.
Cybercriminals target Real Estate precisely because of the large sums of money involved in transactions.
WireFraudPrevention.org reports that approximately 35-50% of all wire fraud cases stem from real estate transactions, especially during closing processes.
In the decade ending in 2023, real estate wire fraud grew 50 times from $9 million to $446 million in annual losses reported to the FBI Internet Crime Complaint Center.
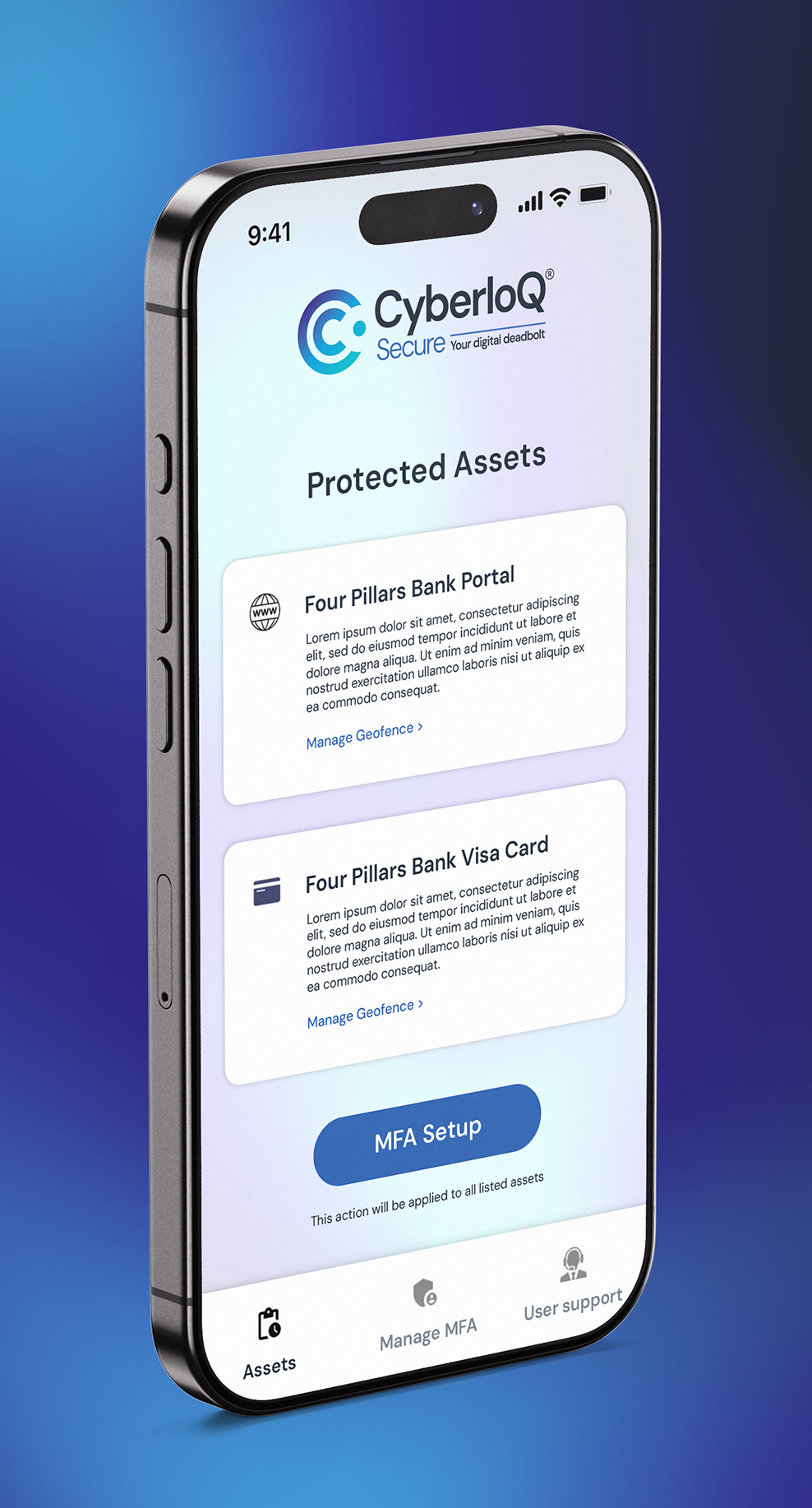
CyberloQ Secure® is zero-trust identity verification that helps protect you against fraud resulting from identity impersonation based on stolen account credentials.


Strong Customer Authentication (SCA) utilizes a combination of challenge factors that rely on what is unique to each individual authorized to access your systems and data:
Whether it’s an Agent remotely accessing your network while traveling, a Transaction Coordinator updating the details of a Listing, a buyer accessing your Portal to verify wiring instructions, or any other type of activity involving sensitive operational system and client data, CyberloQ Secure® enforces SCA to verify the identity of your trusted associates and customers every time they initiate a digital interaction with your organization, without compromising their user experience.
Our Face or Fingerprint challenges utilize something you alone are.
We challenge the user to verify their identify by responding to their device’s biometric request. This allows us to block unauthorized access to your protected resources, even if the device is stolen.
Our Voice Verification solution utilizes something you alone are.
We send a unique Voice Passcode and challenge the user to verify their identity by speaking that code into their mobile device. Again, this blocks unauthorized access to your protected resources, even if the device is stolen.
Our innovative Location Verification utilizes something you have. We determine the User’s real-time location and compares it to any geographic areas established as permissible – or not – for that user.
Access is allowed only from the User’s in possession of their registered device and within authorized locations.
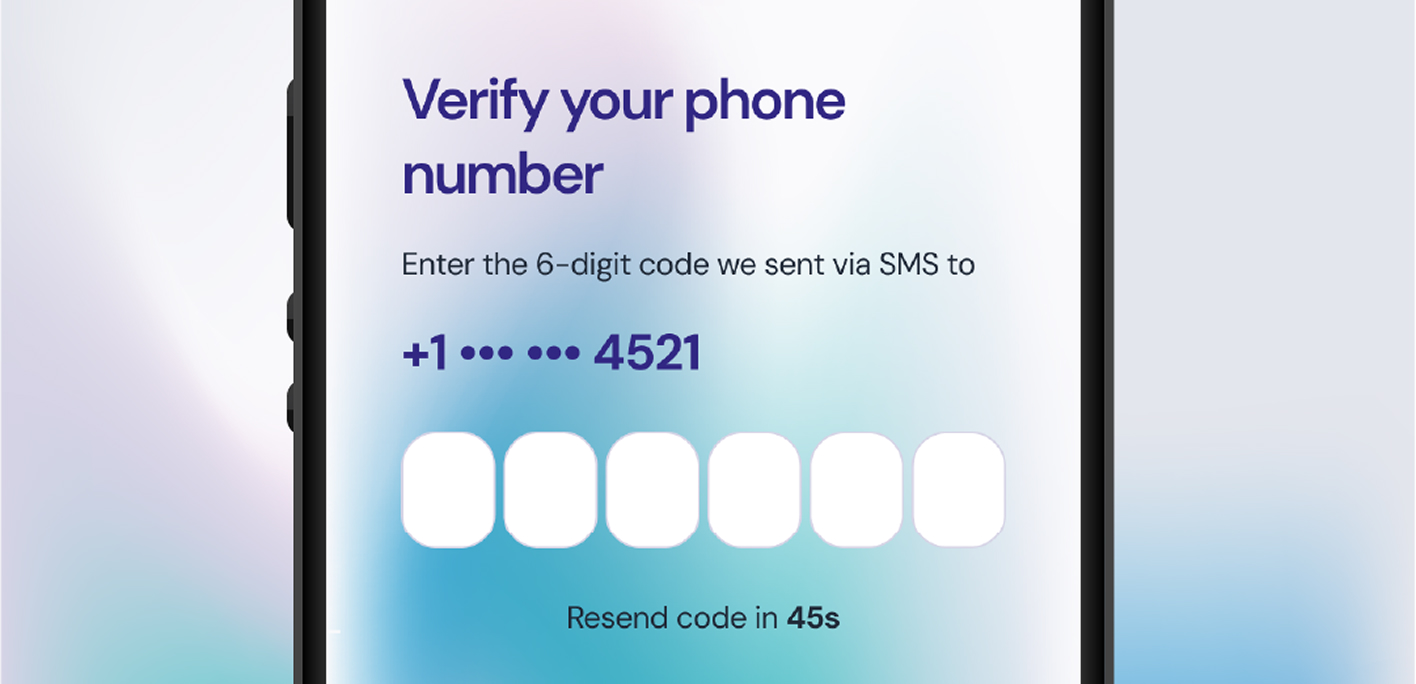
Our OTP Verification utilizes something you know. We send a unique OTP and challenge the user to verify their identify by typing that code into their mobile device.
Like a face or fingerprint, OTPs are a familiar and effective method of blocking for unauthorized access to your protected resources.
Implemented through a straightforward and seamless API integration with your organization’s Identity Management System, the CyberloQ Secure® MFA sits between your users and your digital resources, continuously verifying the user’s identity with each attempt to access a protected digital resource.
Following are just a few of the operational use cases for CyberloQ Secure® that your Real Estate organization might elect to implement.
THREAT: A cybercriminal attempts to impersonate one of your legitimate users – e.g., an Agent, an internal staff member, or a 3rd Party partner from a Title Company, Escrow Agency, a Lawyer, etc. – by using stolen access credentials to log into your backend business portal to shutdown your business operations, to steal your data, or to hijack your data – think ransomware.
RESPONSE: The criminal’s login attempt triggers the push of a CyberloQ Secure® MFA challenge to the legitimate User’s registered device. Aware that they did not initiate the login attempt, the legitimate User simply intentionally fails the MFA challenge, thereby denying access to the criminal.
OUTCOME: The benefits from utilizing the CyberloQ Secure® MFA in this manner are threefold: The legitimate User is immediately made aware that their login credentials have been compromised, they have successfully blocked an unauthorized access to your Brokerage’s systems and data and, finally, they have directly prevented the cybercriminal’s intended financial and reputational damage to your Brokerage.
NOTE: the same Threat-Response-Outcome scenarios apply to other organizations participating in the Real Estate ecosystem. For example: