CyberloQ Secure® multi-factor authenticator (MFA) delivers the next-generation of identity verification capabilities that turn your smartphone into the ultimate gatekeeper for your sensitive data and financial transactions.

Sitting at the intersection of security and convenience, CyberloQ Secure® seamlessly integrates with your existing Identity & Access Management (IAM) stack to deepen your cybersecurity with robust yet user-friendly defenses.
Zero Trust is a strategic mindset: “never simply trust, always actively verify.”
Our patent pending proprietary identity verification protocols implements the Zero Trust strategy by enforcing real-time strong customer authentication at every digital access point.
This brief video demonstrates how CyberloQ Secure® helps your organization build unbreakable systems for safeguarding your digital resources, and your brand.
Strong Customer Authentication (SCA) utilizes a combination of challenge factors that rely on what is unique to each of your users:
Whether it’s an employee remotely accessing your network, or a customer making a purchase with a Credit Card, or any other type of activity involving sensitive data or financial transactions, CyberloQ Secure® enforces SCA to verify the identity of your trusted associates and customers every time they initiate a digital interaction with your business, without compromising their user experience
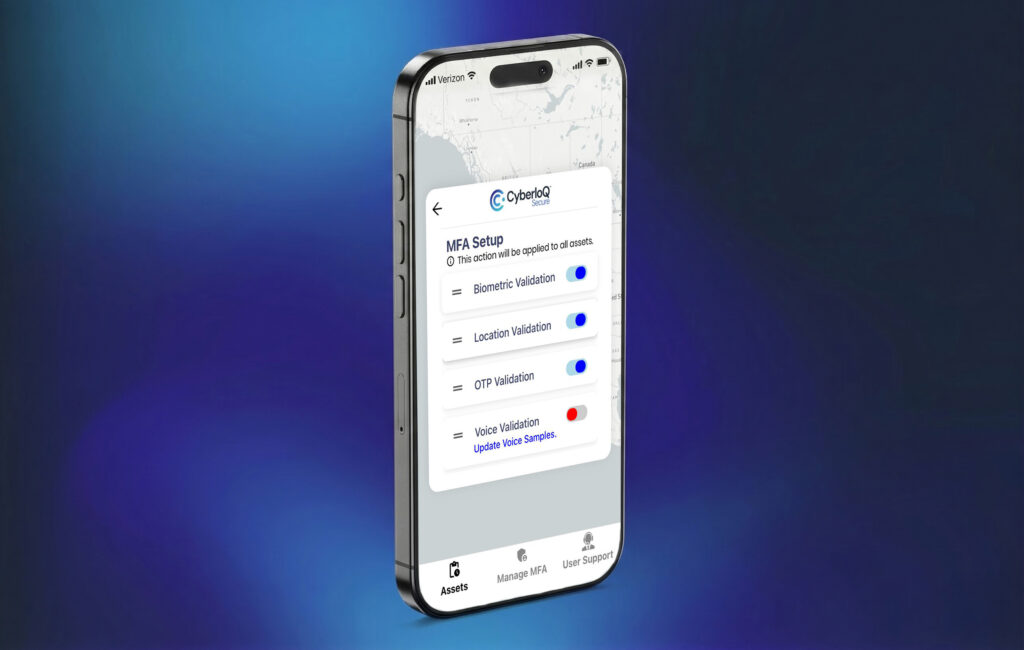
Our Face or Fingerprint challenges utilize something you alone are.
We challenge the user to verify their identify by responding to their device’s biometric request. This allows us to block unauthorized access to your protected resources, even if the device is stolen.
Our Voice Verification solution utilizes something you alone are.
We send a unique Voice Passcode and challenge the user to verify their identity by speaking that code into their mobile device. Again, this blocks unauthorized access to your protected resources, even if the device is stolen.

Our innovative Location Verification utilizes something you have. We determine the User’s real-time location and compares it to any geographic areas established as permissible – or not – for that user.
Access is allowed only from the User’s in possession of their registered device and within authorized locations.
Our OTP Verification utilizes something you know. We send a unique OTP and challenge the user to verify their identify by typing that code into their mobile device.
Like a face or fingerprint, OTPs are a familiar and effective method of blocking for unauthorized access to your protected resources.





According to the Cisco Talos ‘2024 Year in Review report‘, attackers used valid credentials to access corporate networks in almost 70% of cybersecurity incidents.
The CyberloQ Secure® platform focuses on one thing: empowering your organization to prevent unauthorized access to the systems and applications that run your business.
To meet the requirements of strong customer authentication, CyberloQ Secure® combines standard one-time passcode challenges with additional challenges based on the user’s mobile device itself, and the unique biometric characteristics of their face, fingerprint and voice.
The unique geofencing functions at the heart of the CyberloQ Secure® platform enables you to define and assign authorized geographic zones to discrete user-asset combinations
These geofence assignments automatically block attempts to access your assets (e.g., websites, bank cards, databases etc. from unpermitted locations.
In a world where cyber threats never sleep, your organization requires security tools that keep you one step ahead. CyberloQ Secure® is an innovative approach that:
Use CyberloQ Secure® to maintain and enforce a zero-trust security protocol that supports regulatory requirements for protecting your critical assets, all while reducing friction for legitimate users.
In today’s only transaction environment, stolen user credentials are rapidly becoming the most common entry point for data breaches and financial fraud
Implementing CyberloQ Secure® will set you apart from your competition when it comes to protecting the identity and assets of your trusted associates and customers
For Software providers, integrating CyberloQ Secure® into your SaaS offerings strengthens your existing authentication and access controls.
Delivering this enhanced security increases your overall value proposition to your clients.
The CyberloQ Secure® Platform is a secure, cloud-based, fully managed multi-factor authentication solution that easily integrates into your existing security infrastructure to meet your user identify verification needs.
CyberloQ Secure® is a low-effort, low-cost API integrations that gets you quickly up and running with significantly enhanced identity verification and user authentication.
Get answers to common questions about our industry-leading strong customer authentication platform.
These are the four core use case categories where CyberloQ Secure® delivers the most impact. Each scenario combines geolocation intelligence, device trust and adaptive MFA in different ways to match your risk profile and regulatory needs.
These are the four core use case categories where CyberloQ Secure® delivers the most impact. Each scenario combines geolocation intelligence, device trust and adaptive MFA in different ways to match your risk profile and regulatory needs.
These are the four core use case categories where CyberloQ Secure® delivers the most impact. Each scenario combines geolocation intelligence, device trust and adaptive MFA in different ways to match your risk profile and regulatory needs.
Our security experts are ready to provide personalized guidance.